When does CTDPA take effect and who does it apply to?
The CTDPA or Connecticut data privacy act comes into effect on July 1st 2023 and applies to Connecticut businesses who process personal data on 100,000 Connecticut residents or 25,000 or more if businesses gross revenue is based on 50% or more on selling their personal data. The law does not apply to B2B processing transactions, employee information, encrypted personal data, public information (as found openly on internet listings for example) or to personal data such as health data or credit reporting as covered by federal laws such as HIPPA, GLBA & FCRA.
Why are the key consumer rights of CTDPA?
The Connecticut privacy law is similar to other state laws like California’s CCPA/CPRA laws in that it provides consumer access rights to their data. These rights include;
- The right to obtain a copy of their data
- The right to delete personal data
- The right to correct their personal data
- The right to port (move) their data to another vendor
- The right to appeal a decision by the data controller not to provide their data
- The right to opt-out of sale or profiling for targeted ads
When a consumer makes such a request it’s refered to as a DSR or Data Subject Request and is expected to be facilitated within 45 days of the request. Businesses may apply for a 45 day extension in some cases.
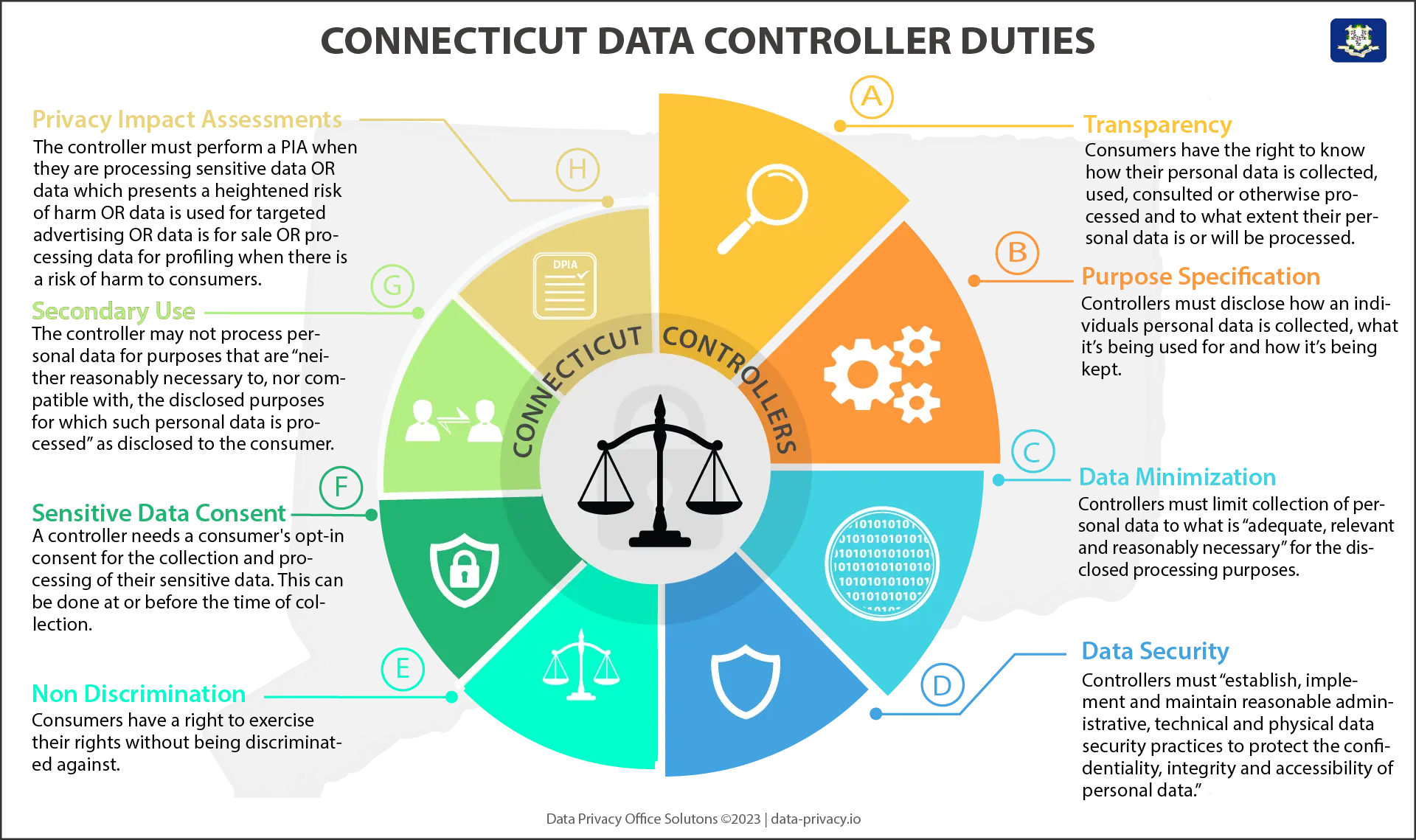
What are the data controller responsibilities under CTDPA?
Data Controllers make decisions on the when and how personal data is processed and are expected to abide by data protection principles (related article) which stem from GDPR regulation in Europe and other pre-existing state laws. These requirements include;
- Data Minimization: Controllers must limit collection of personal data to what is “adequate, relevant and reasonably necessary” for the disclosed processing purposes
- Transparency: consumers have the right to know how their personal data is collected, used, consulted or otherwise processed and to what extent their personal data is or will be processed.
- Purpose Specification: Controllers must disclose how an individuals personal data is collected, what it’s being used for and how it’s being kept.
- Data Security: Controllers must “establish, implement and maintain reasonable administrative, technical and physical data security practices to protect the confidentiality, integrity and accessibility of personal data.”
- Secondary Use: The controller may not process personal data for purposes that are “neither reasonably necessary to, nor compatible with, the disclosed purposes for which such personal data is processed” as disclosed to the consumer.
- Privacy Impact Assessments: The controller must perform a PIA when they are processing sensitive data OR data which presents a heightened risk of harm OR data is used for targeted advertising OR data is for sale OR processing data for profiling when there is a risk of harm to consumers.
What is considered personal data under the law?
The Connecticut data privacy law covers two classes of personal data. Personal data and sensitive personal data. Personal data includes basic information like name, address. DOB, SSN, passport no and drivers license no while sensitive personal data is more expansive. It includes, religious beliefs, trade union membership, citizenship data, sexual orientation, genetic or biometric data used for identification, childrens data, health conditions & diagnosis and precise geo-location data.
Who enforces CTDPA and what are the Fines?
The office of the attorney general in Connecticut currently led by William Tong is responsible for CTDPA enforcement. Fines can be issued for up to $5,000 per wilful violation. There is no private right of action as available in states like California. Note that in cases where Conneticut residents are seriously impacted by a breach, other agencies like the FTC may instigate their own sanctions which are usually much higher in the penalty scale. The same maybe said of class action suits by attorneys for which Connecticut residents are a party to.
What privacy notices are required under CTDPA?
Businesses are required to provide clear and transparent notice to customers at or before the time of collection of personal data. This means that if a controller sells personal data to third parties or processes it for targeted advertising, they must implement the following;
- A clear and conspicuous link on their website that enables consumers to opt out of either of the above activities
- As of January 1st, 2025, controllers must allow consumers to opt out of personal data collection to be used for targeted advertising, or the sale of their personal data, via an “opt-out preference signal”
- This signal will be captured by a technology such as a consent management platform (CMP) which supports global privacy controls (GPC’s)
- Consumers must be notified of any sale of data or targeted advertising
- Businesses must also notify customers of the categories of data they collect on them and purpose for processing
- They must provide directions on how consumers can exercise their privacy rights and rights of appeal
- They must provide details on any 3rd parties data is shared with and the categories of data shared, and;
- An active email address for the data controller.
What are the rules for data processors under CTDPA?
Data processors under Connecticut data privacy law is a person that processes personal information on behalf of a business (data controller) and that receives from or on behalf of the business a consumer’s personal information for a business purpose.
CTDPA requires that a contract must be in place between a controller and a processor which governs the processor’s data processing procedures with respect to processing performed on behalf of the controller. This ‘Contract’ must include the following;
- Instructions for processing data;
- The nature and purpose of processing;
- The type of data subject to processing;
- The duration of processing; and
- The rights and obligations of both parties
In addition, the processor is required to;
- Ensure that each person processing data is subject to a duty of confidentiality with respect to the data;
- At the controller’s discretion, delete or return all personal data to the controller as requested at the end of the provision of services;
- Upon the reasonable request of the controller, make available to the controller all information in its possession necessary to demonstrate the processor’s compliance with the obligations of the Act;
- After providing the controller an opportunity to object, engage any subcontractor pursuant to a written contract that requires the subcontractor to meet the obligations of the processor with respect to personal data; and
- Allow, and cooperate with, reasonable assessment by the controller.
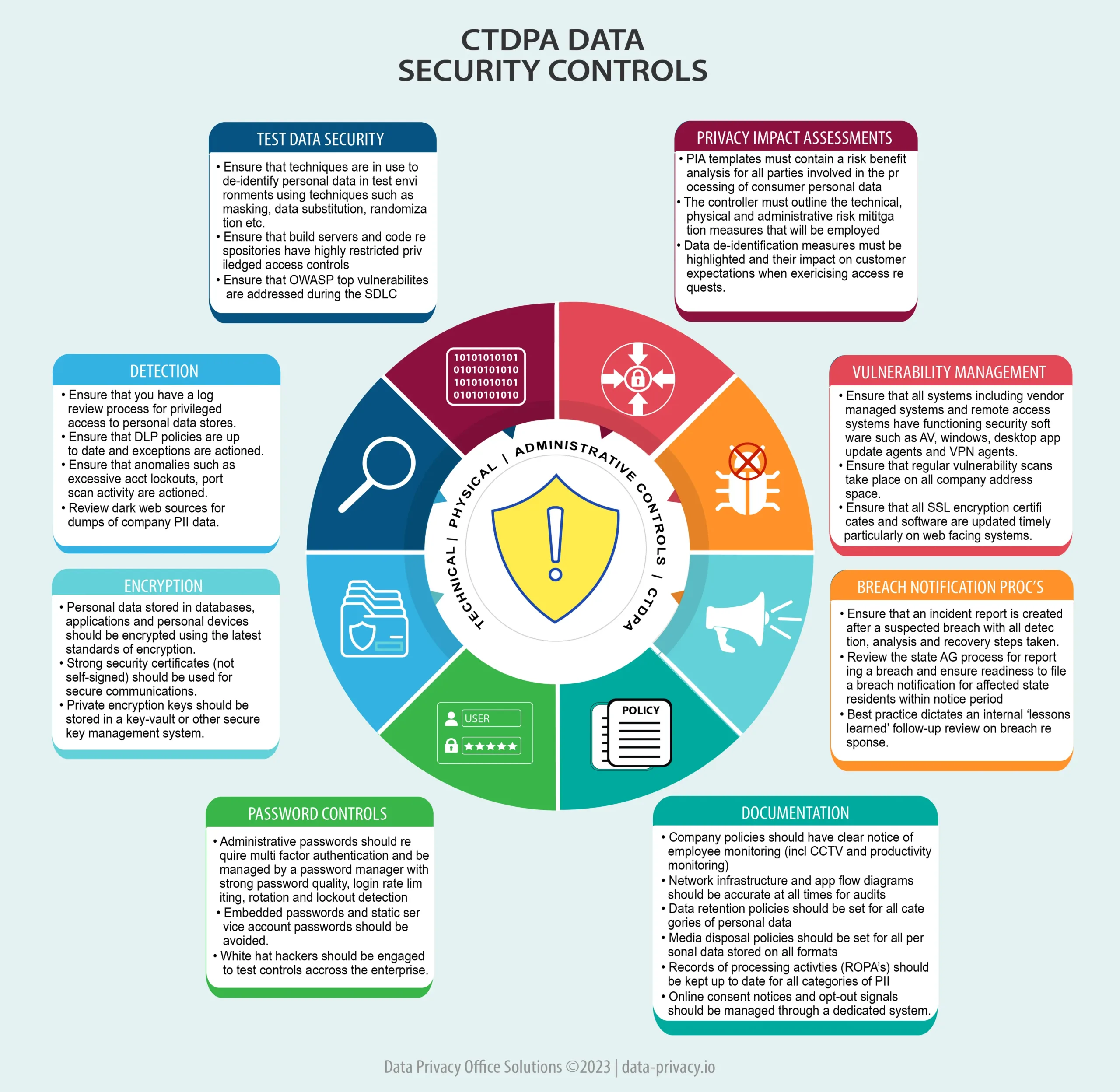
What are the expected security controls under CTDPA?
CTDPA has a general requirement for data controllers to “establish, implement, and maintain reasonable administrative, technical, and physical data security practices to protect the confidentiality, integrity, and accessibility of personal data appropriate to its volume and nature”. These requirements are largely met by adherence to industry security frameworks such as NIST Cyber Security Framework, ISO 27000 and CIS Benchmarks. Frameworks like these, describe an Information Security Management System (ISMS) which is really an extensive list of security controls such as establishing a security function (administrative control), implement encryption for stored personal data (technical control) and installing keycode entry doors (physical control).
Encryption is a key control in that CTDPA dictates that encrypted data which ensures that personal data which is de-identified by encryption techniques is not in scope of CTDPA.
Privacy impact assessments are also a requirement under the act when any of the following conditions are met; processing of sensitive data or when data represents a heightened risk of harm or if data is for sale or targeted advertising. See the diagram below for a full list of expected controls under CTDPA.
What notice periods are important under the data privacy act?
Key timings for the Connecticut data privacy act include
- 45 days to respond to a data subject request (DSR/DSAR) with a possible 45 day extension
- 60 days to report a breach on the OAG website Report a Breach form
- 60 days right of appeal of a controllers denial to facilitate an access request
- 60 days to cure / remedy a complaint
- July 1st CTDPA enactment date
What about CTDPA training?
Employees are expected to be trained on Connecticut data privacy law and risks at least annually. If you need a convenient powerpoint based training solution, check out our Data privacy awareness training for employees of Connecticut businesses.