Train your staff the economical way with our easy to understand ISTA accredited laptop security awareness training presentation. This training covers physical security measures, password security, encryption, software security and more in a high quality presentation designed to minimize risks fast.
Laptop Security Awareness Presentation Guide for Employees
$19.00
Description
Laptop loss and thefts are in the top 5 list of risks for organizations with respect to data breaches. Last year 600,000 laptops were lost in US airports alone generating more incidents than any other category of security problems. Many of these losses and much of the hassle of statutory notifications is avoidable with some common sense tactics. Our ISTA (International Security Training Assoc) GRC accredited laptop security awareness training guide for employees is a compact, easy to follow presentation gives laptop users the heads up they need when using a valuable corporate asset. The presentation covers the important basics of physical security, drive encryption, password security, backup strategy, secure file deletion and more for Windows and Mac devices. The full list of contents includes;
- Laptop physical security (Kensington locks, unattended vehicle guidance, asset tags, privacy screens, locked cabinets, GPS tracking, find my device tracking (for Windows and Macs)
- Drive encryption methods including FDE native O/S examples.
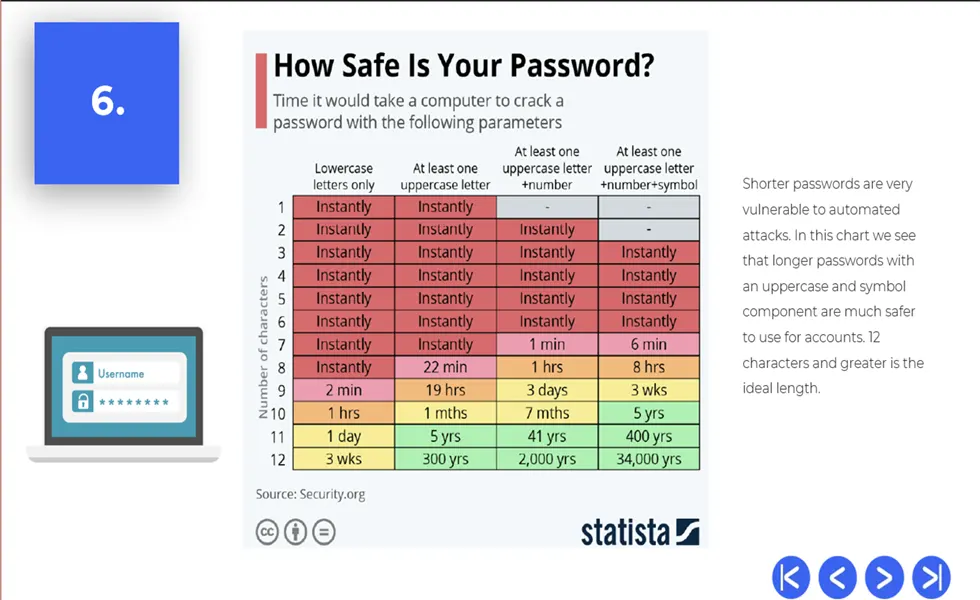
- Complex password composition with examples and statistics on breakability.
- Laptop WiFi risks with recommendations on security settings.
- Laptop use good practices including guidance on avoiding device sharing, OS/Browser/App patching.
- Laptop data backup strategy (Local & Cloud) with incremental and full backups.
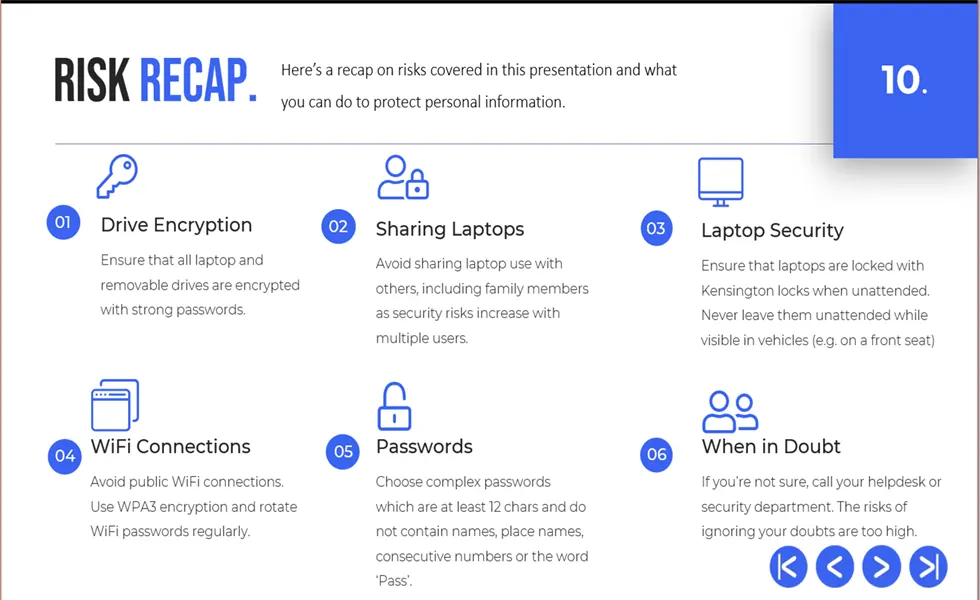
- Risk recap to review the above concepts.
GRC Training Requirements
Up to date security training is required by all security GRC regulations, standards and certifications today and is a proven method of reducing human risk. Yet, statistically companies tend to use the same training approach and content from year to year leading to higher and higher incidents of successful attacks. Studies have shown a high degree of user disengagment with security training when similar training is administered again and again. This is why a new approach is needed, read the benefits.
Our presentation style training is a simple, economical alternative to other training offerings out there. Read the benefits below.
Benefits
Benefit of this training includes;
- We use plain language to communicate and raise awareness for laptop cybersecurity topics.
- No subscription, monthly fees or hidden charges.
- A low-cost solution with no integration requirements into your environment.
- Easy to deploy the presentation through email or on users home drives, network share drives etc.
- Coverage of the main risks at a high level so most employees will understand.
- Teaches students on the value of data on laptops.
- Teaches students on the very real risks associated with weak passwords.
- Designed for onsite and remote workers while using work or personal assets.
- Includes recap to reinforce concepts.
- Easy to customize as it’s a powerpoint format.
- ISTA Accredited training.
We also offer coding support if you need custom features using our Contact Us page.
What’s Included?
1 PowerPoint deck in pptx format; Approx 14mb in size.
Use Cases?
This training powerpoint and material has a wide range of uses such as;
- As new material for your cybersecurity awareness program.
- As a mandatory training for employees who receive laptops in your org.
- As evidence of regulatory compliance with a range of GRC regs, frameworks and certs.
- HR Onboarding (New Hires).
- As a compliment to some of our security presentations available on our store.
- As a form of new training for stale content in your organization, a common reason why employees disengage from security training.
Features
- Easy to understand coverage of laptop security risks in a 10 minute presentation.
- High quality graphics for a professional look and feel.
- Latest (.pptx) format for maximum compatibility with desktop and mobile players.
- Economic file size for easy email distribution.
- Easy to use navigation controls.
Payments
Payments will appear as DPO Solutions. Refunds are limited to technical that cannot be resolved and double billing issues. Be sure to check your junk mail if you haven’t received your download link before contacting us.
Why isn’t the training free?
We have reviewed the many presentation training decks out there on free slide sharing sites and feel that they are not fit for purpose when training staff on such an important area as cybersecurity. This presentation involved over 60 hours of development including graphics, research, coding, animation development and peer review by industry experts.
Other Products & Development
We stock a range of GRC products in our Store covering areas such as general cybersecurity awareness, data privacy awareness, payment card compliance, AI and more which have a similar look and feel to this training.
Based in Ireland, we have also built training sets for organizations who want training solutions in multiple domains (IT & Financial regulatory). We can assess gaps in your current training portfolio and build low cost, high impact solutions based on your GRC requirements. Use the contact us page to learn more about these options.
Copyright
Resale of this product is prohibited without express permission of DPO solutions.





Additional information
| Description | An essential cybersecurity awareness PowerPoint training for employees with end of module quizzes and examples for trainee comprehension. Extensive coverage of phishing risks, identity theft and device security with easy to understand advice on risk prevention. Includes quiz, glossary and external references. |
|---|
Price
$19







Reviews
There are no reviews yet.